MongoDB Realm #
Within the realms of the Cosync JWT application, the MongoDB Realm tab serves as a pivotal bridge, establishing a connection to a MongoDB App Services application housed within the MongoDB Portal. Here, within the application detail, the developer wields the power to configure a MongoDB App Services application, a versatile playground for the CosyncJWT service or the Cosync Storage module. This tab stands as a vital conduit, enabling seamless integration and configuring the MongoDB App Service Application to harness the full potential of Cosync’s offerings.
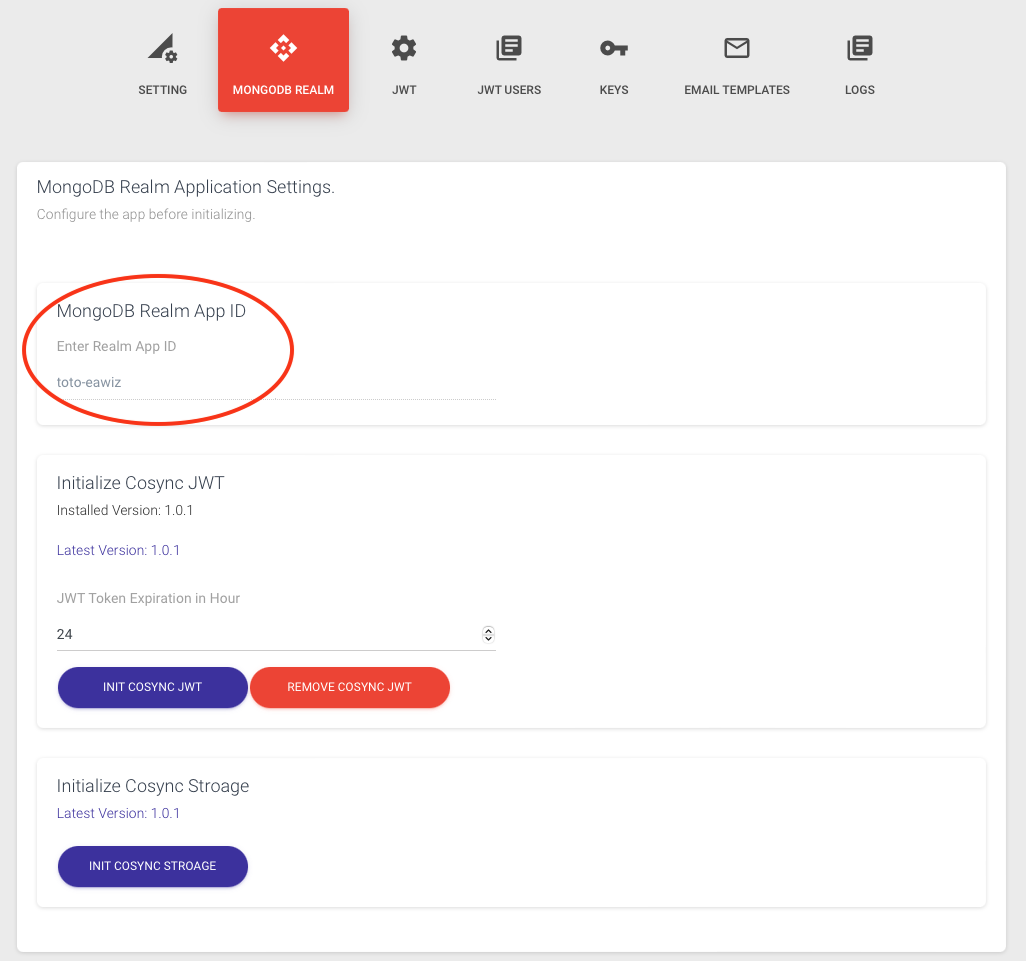
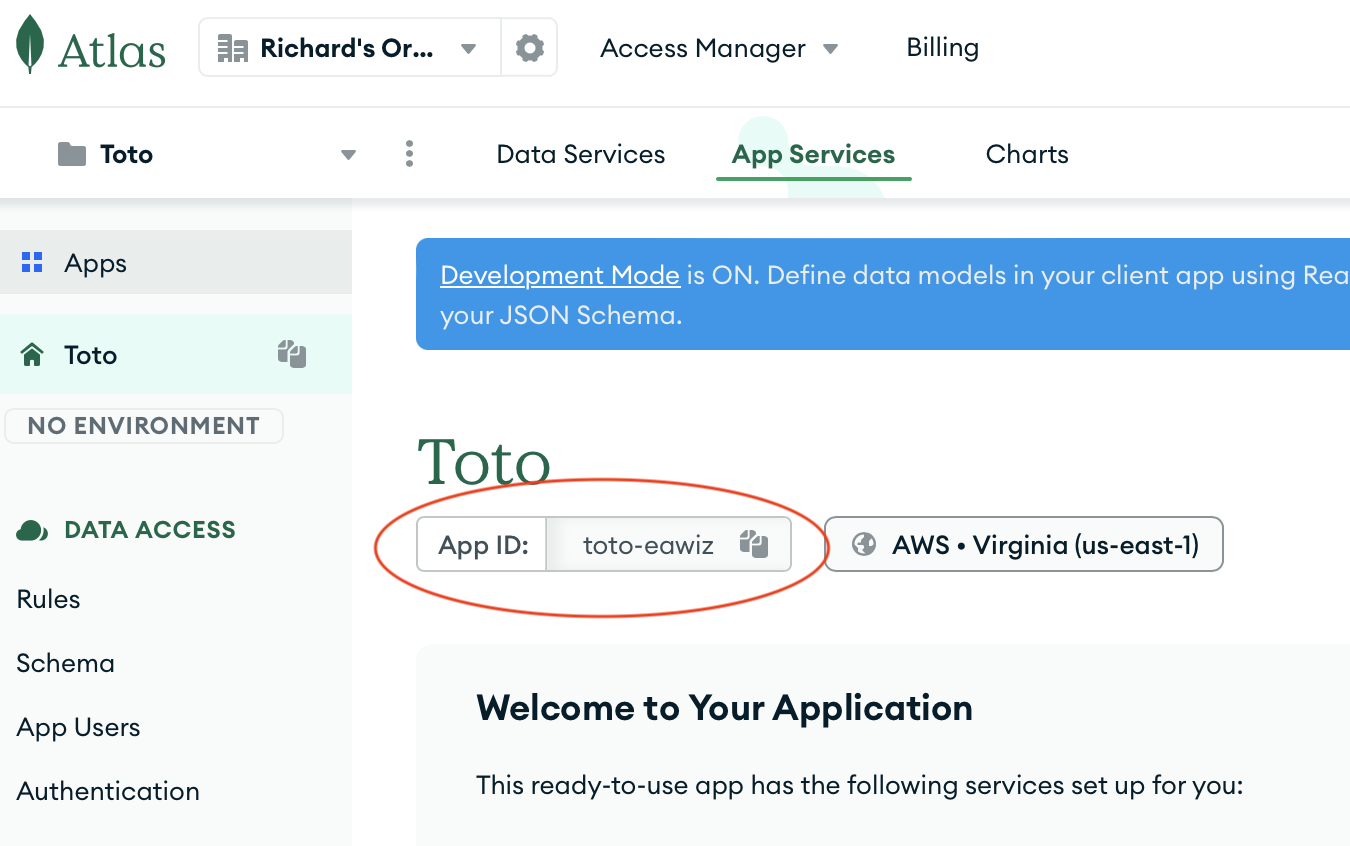
Within the context of application integration, the MongoDB Realm Application Id assumes the role of a fundamental bridge that connects a Cosync-level application with the Realm-level. Introduced and managed by the developer through the Cosync Portal, this critical identifier establishes a seamless connection between the two realms. Its underlying simplicity enables applications to operate cohesively, traversing effortlessly between the Cosync and MongoDB Realm domains. The MongoDB Realm Application Id is retrieved from the MongoDB Portal as shown below.
How to initialize Cosync JWT #
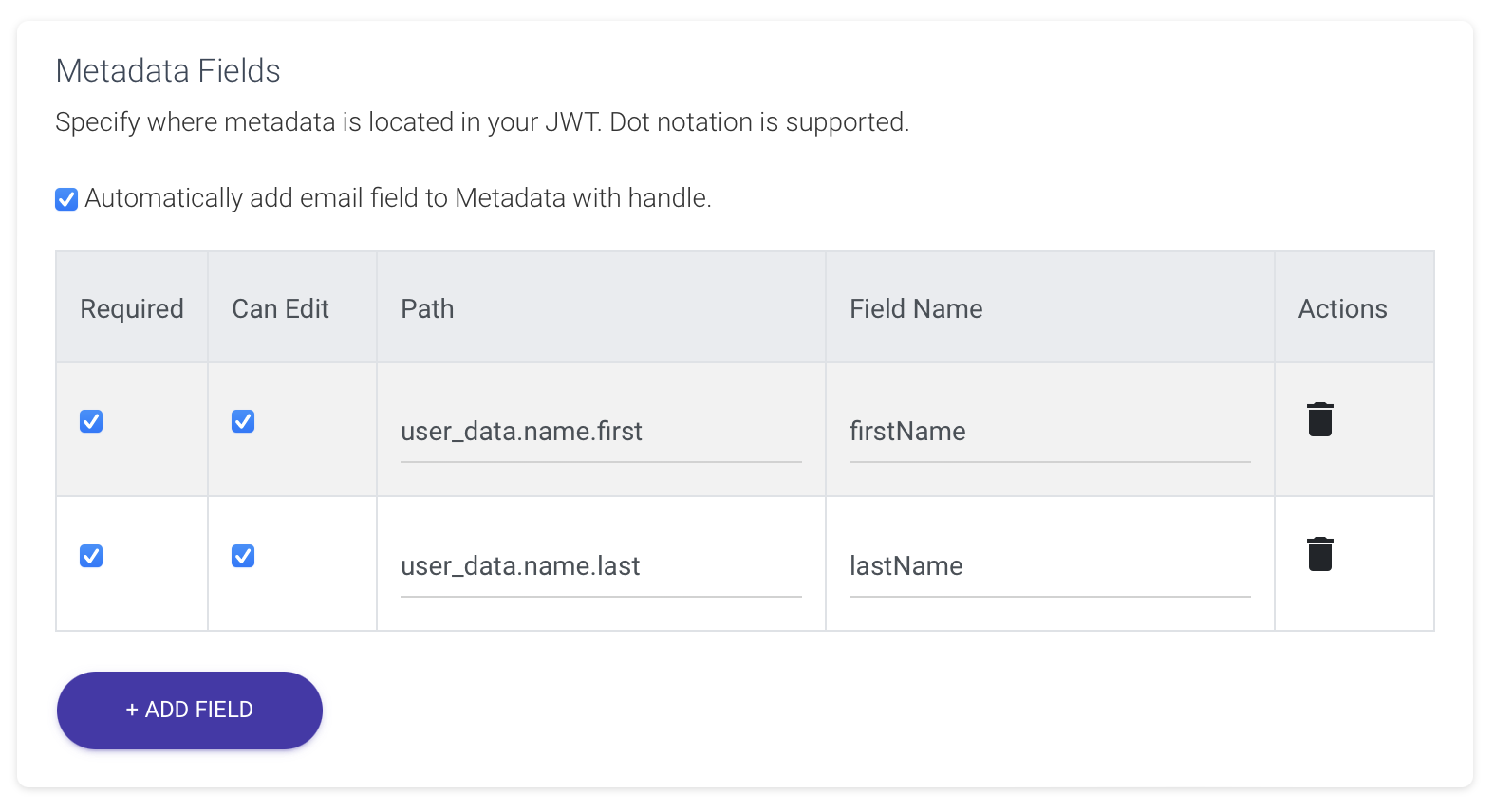
The MongoDB App Services Application initialization with the Cosync JWT authentication system requires just a single click! By clicking the INIT COSYNC JWT button, a dialog box will appear. However, before proceeding, ensure that the correct MongoDB Realm App Id is entered, as indicated above. If you are utilizing the Cosync Sample application, double-check the meta-data in the JWT tab to ensure accurate specification, as demonstrated below.
To initialize the MongoDB App Services Application, press the INIT COSYNC JWT button
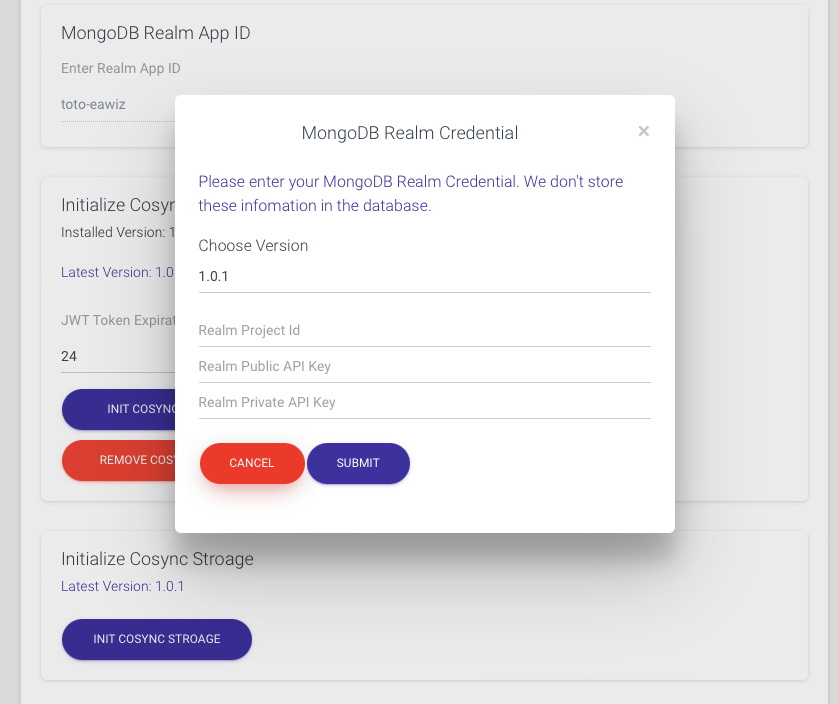
You can retrieve the Realm Project Id, the Realm Public API Key, and the Realm Private API Key as explained in the Get Started section Realm API Keys.
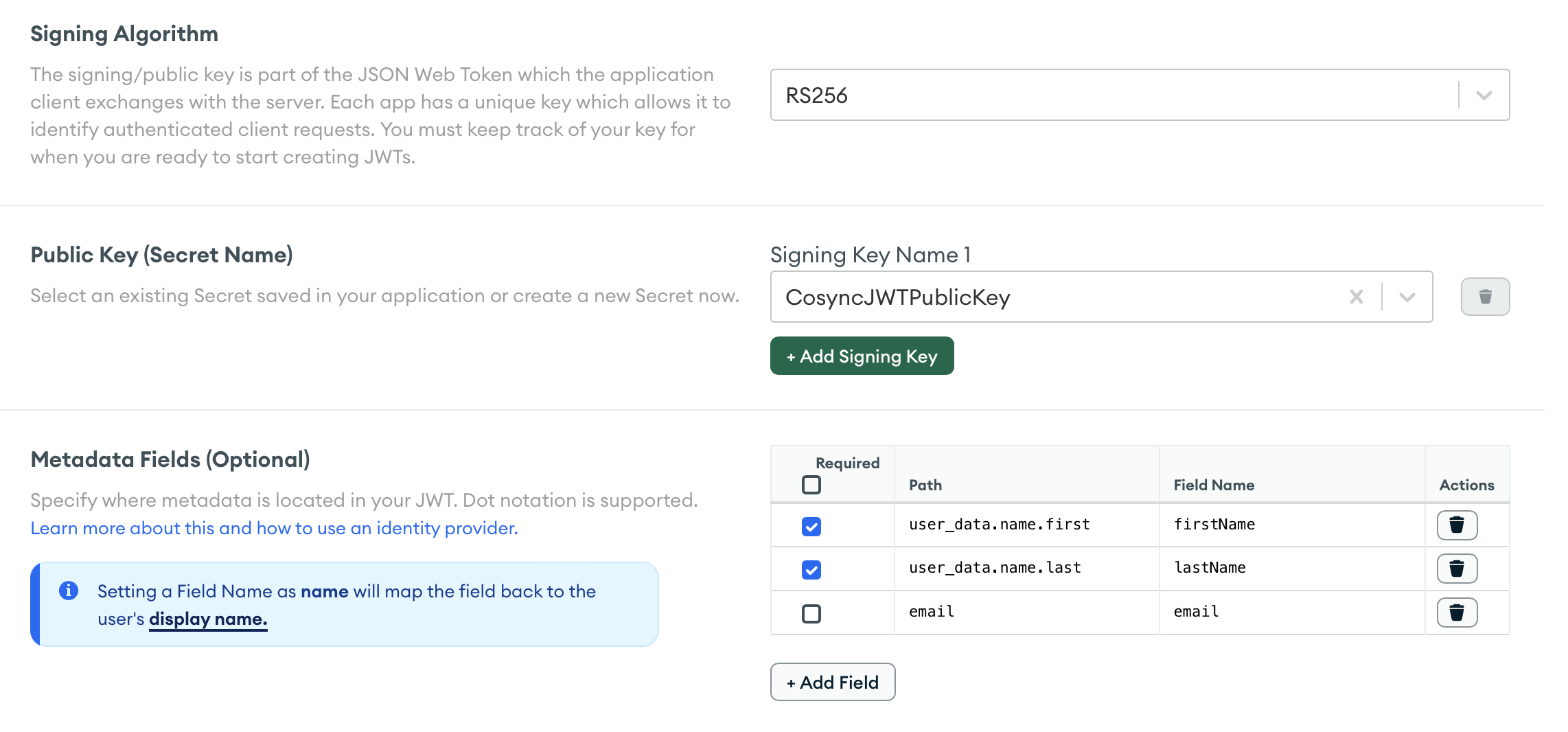
To confirm the successful initialization of the MongoDB App Services Application, navigate to the DATA ACCESS/Authentication tab within the Application section of the App Services in the MongoDB portal. Look for the Custom JWT Authentication section, where you should find a screen resembling the following: