Keys #
The Keys tab in the CoSync Portal holds the RSA public key, which serves as MongoDB Realm’s means to validate the authenticity of the CoSync Auth signing authority. Additionally, it houses the app token utilized to access the CoSync REST Service API.
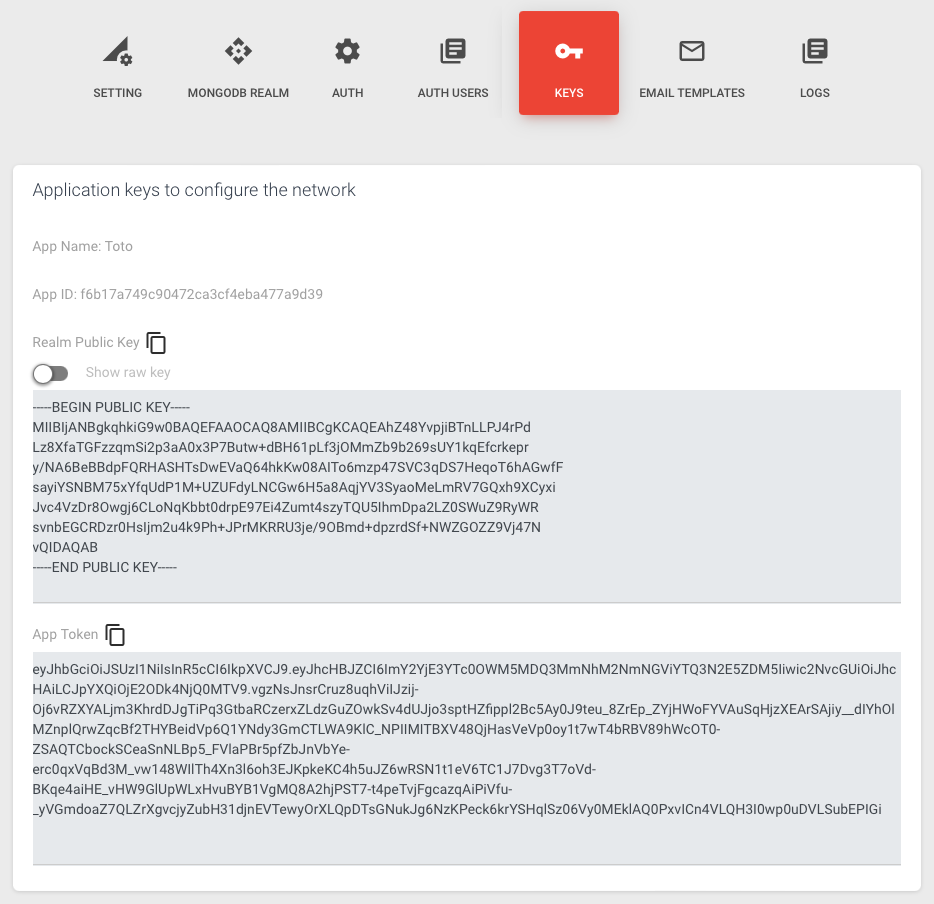
Realm Public Key #
The Realm Public Key field holds the RSA public key linked to the concealed private key of the application. This key is presented in the following format:
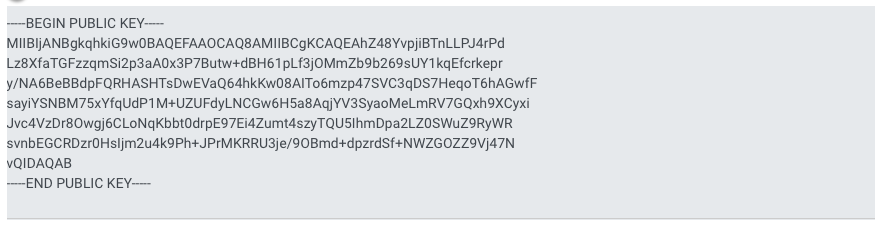
To enable JWT authentication, the crucial step involves copying and inserting the public key in the BEGIN PUBLIC KEY format. This public key is then placed within the JWT Provider tab of the corresponding MongoDB Realm Application. This action effectively activates JWT authentication for the application.
By toggling the Show Raw Key option, you can obtain the raw version of the RSA public key in the following format: [raw key format]. This feature allows developers to access the unmodified representation of the RSA public key for specific purposes within the CoSync Portal.
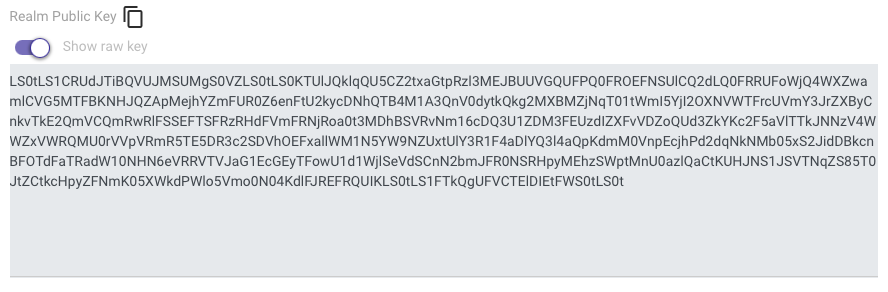
Occasionally, developers require a raw key when invoking a cryptographic library from their code. In such cases, having access to the raw version of the RSA public key proves beneficial, allowing for seamless integration with the cryptographic functions used in their application.
App Token #
The App Token must also be copied and pasted into the constants file of the application’s code. This JWT token plays a pivotal role in authenticating the calling application when interfacing with the CoSync Auth REST API. Ensuring the presence of this token in the constants file is vital for seamless and secure communication between the application and the CoSync Auth API.
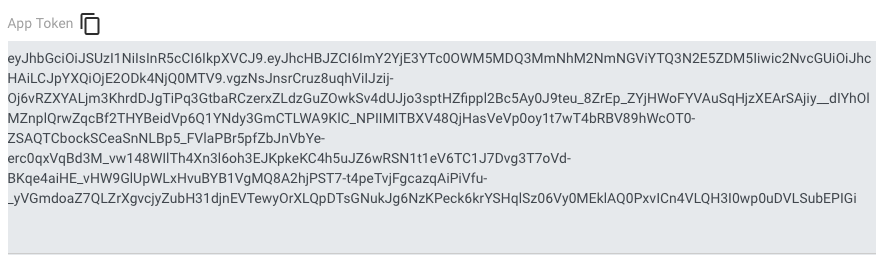
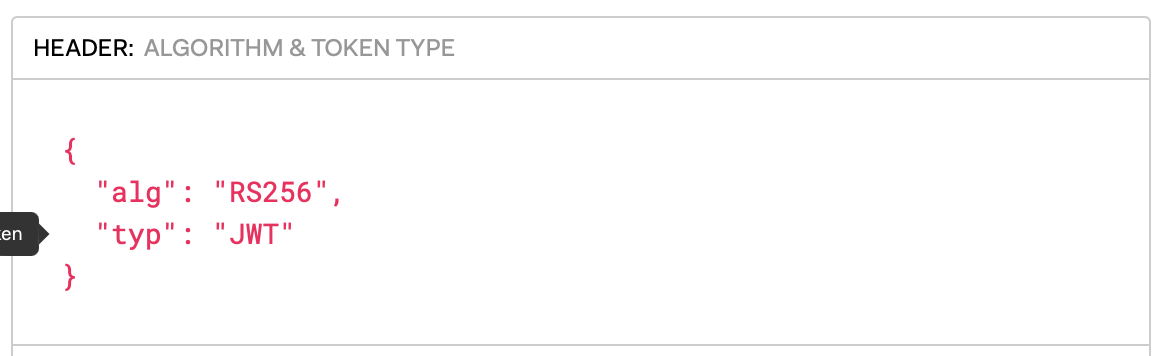
When you visit the website jwt.io, you have the capability to decode the JWT App Token. The header section of this token includes essential information such as: [details of the header information]. This decoding process grants insights into the inner workings and content of the JWT App Token, aiding in its understanding and verification.
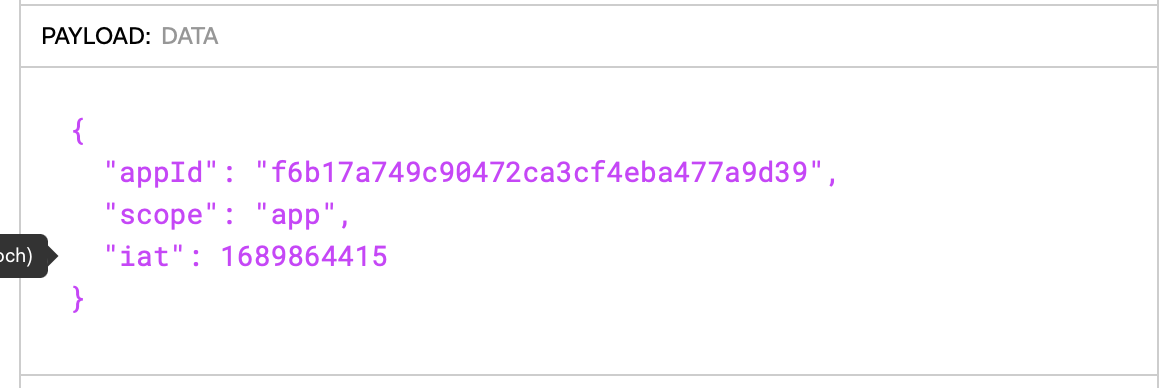
while the payload contains
Due to its signature with the CoSync Auth private key, counterfeiting the JWT App Token becomes extremely challenging, if not near impossible. Rest assured, the CoSync Auth private key responsible for signing the token is securely stored on the CoSync Auth server, ensuring its protection from unauthorized access and potential security breaches.