How to manage an application’s JWT settings
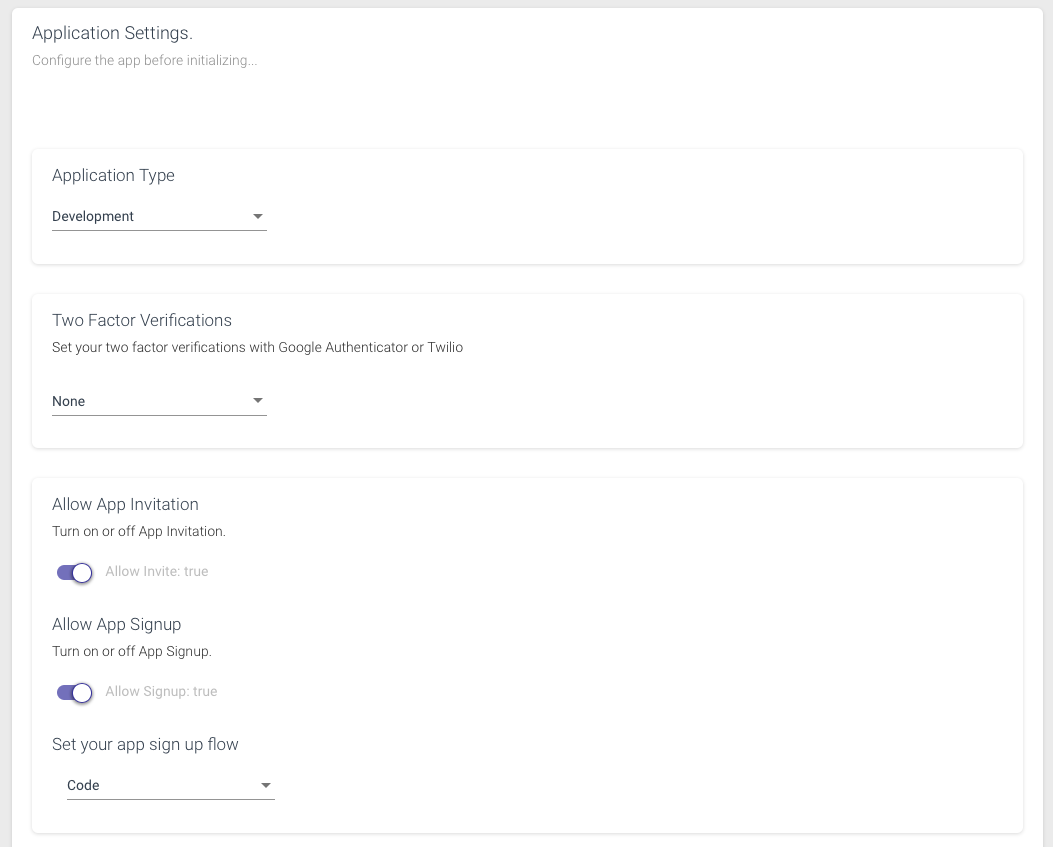
The JWT tab within the CosyncJWT portal is used to manage settings within an application. It presents functionality to
- Turn on two-factor verification
- Allow application invitation
- Allow application signup
- Set signup flow
- Specify the meta-data format
- Password filter
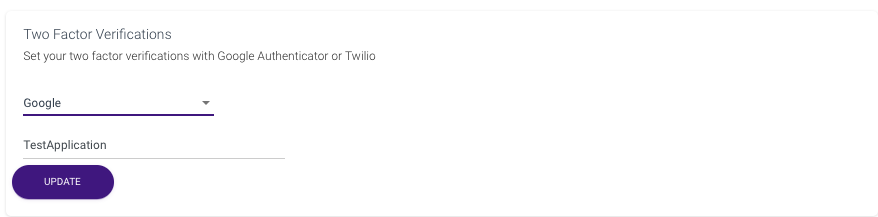
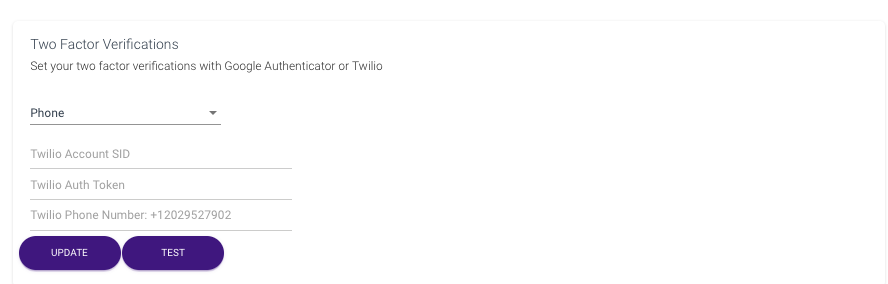
CosyncJWT supports two-factor authentication that provides an extra level of security for users logging into applications. It provides two methods for doing this:
- Google Authenticator app
- SMS login codes sent through TWILIO
The Google Authenticator app has the advantage of being free and ultra secure because the 2-factor codes are rotated every minute. For more information about the Google Authenticator application, please consult the following link.
Another form of two-factor authentication is through SMS login codes that are sent to a user through a developers TWILIO account. For more information about TWILIO see the following link.
A developer can enable two-factor authentication for an application through the Two Factor Verification controls in the Application Settings tab. Select google to enable the Google Authenticator app. The settings allow the developer to enter the heading (in this case “TestApplication”) to be used to identify the application with the Google Authenticator.
To enable SMS login codes to perform two-factor authentication for an application, select phone and enter the following information associated with your TWILIO account:
- TWILIO account SID
- TWILIO Auth Token
- TWILIO Phone Number
This information is only available to developers who have a paid TWILIO subscription. The advantage of using SMS login codes is that they do not require setting up the Google Authentication application. The disadvantage is that each SMS login code cost the developer money. For applications with large user bases, this cost can add up.
Onboarding into the application is controlled through invitation and signup. Both which can be enabled/disabled through the application settings tab. A signup mechanism allows users to onboard into the application directly. The invite mechanism requires that a new user be invited into the application by a user that is already registered with it. The invite mechanism is typically used by application that want to maintain tighter control over those users that belong to it. Both the invitation and signup methods work by sending an email to the new user with a code to verify his/her identity.
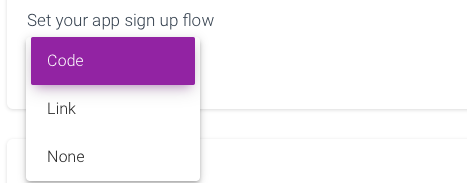
The App Signup Flow determines if and how a user signing up to an app verifies his/her identity. There are three possible choices here:
- none
- code
- link
If none is selected, users can sign up to the application without verification. If code is selected, users are sent a code to their handle to verify their identity and have to enter the code in a secondary signup phase. If link is selected, the user handle is sent a link, which the user can click on to confirm their identity. The HTML of the link landing page can be configured by the developer.
Metadata Fields is used to specify the meta field information that is passed in the authenticating JWT token for the user. For more information about meta data fields as they relate to MongoDB Realm JWT providers, please consult the following link MongoDB JWT Meta Data Fields.
Meta data is used to store information about each user and is refreshed in the Realm data base each time a user logs in. It is stored in the User Object of the logged in user inside Realm. Inside server functions, this meta data can be accessed from the data property of the user object. The meta data is also stored in the JWT token as well.
In the CosyncJWT portal the developer must specify each meta data field using a path and a field name. The path uses a dot notation and specifies a full path of the embedded JSON object within the JWT token. The field name is used to specify the meta data field as it is presented in the data property of the Realm user object. The developer can also specify whether the meta data field is required or not. Users will not be able to onboard with CosyncJWT unless all required meta data fields are specified.
In addition to specifying metadata that is passed by the user at time of signup and/or registration in response to an invite, the developer can also specify metadata that is passed by the inviting user to the invited user. This is the Invite Metadata Fields. If specified, the inviting user will attach meta data that conforms to the specification in the Invite Metadata Fields definitions that will be bundled into the invited user’s metadata within the JWT token at the time of registration.
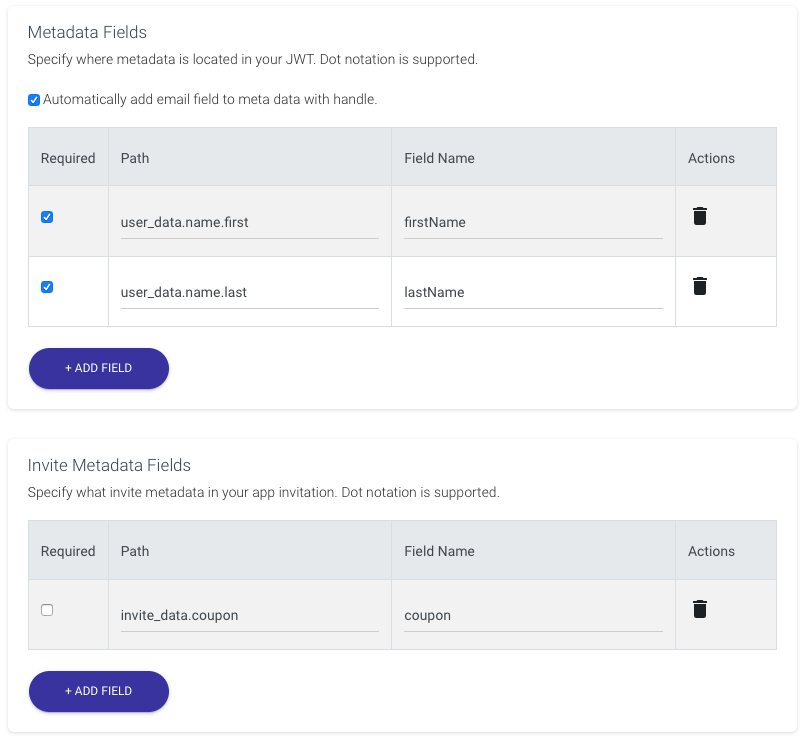
CosyncJWT also includes a check box Automatically add email field to meta data with handle. If this is checked, the user’s email property will be included as part of the JWT authentication token. Unless this is specified, the Name of the user in the Realm Application Portal will be unknown. The developer can alternatively specify a required name meta data field, and MongoDB Realm will use that instead.
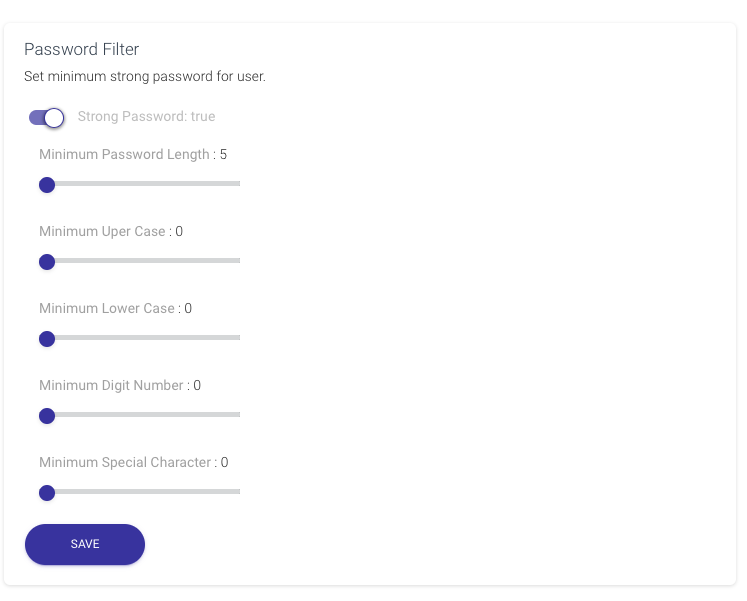
Password filtering is used to impose password requirements on application users when they onboard or change their password. Password filtering is implemented on the client side because the server only ever receives the MD5 hash of the password for security reasons. However, the developer specifies the password filtering parameters on the server side, which are saved as part of the application settings. The client side will query these filtering parameters and implement the password filtering requirements on behalf of the application. Password filtering can either be turned on or off. If turned on, there are a number of filtering parameters that regulate how a password should be formed, these include:
- minimum length
- minimum upper-case letters
- minimum lower-case letters
- minimum number of digits (0…9)
- minimum special characters
The special characters include @, %, +, , /, ‘, !, #, $, ^, ?, :, (, ), [, ], ~, `, -, _, ., and ,